Before we directly jump to the configuration part, let me first explain what is SSL/TLS. SSL and TLS are cryptographic protocols that provide authentication and data encryption between different communication endpoints (e.g., a client connecting to a web server), with SSL the predecessor to TLS. Every few years we see that the new versions of SSL/TLS is released to address the security vulnerabilities (e.g., BEAST, POODLE, DROWN) and support the strongest and most secure cipher suites. The latest being TLS 1.3, which was just approved by the IETF (Internet Engineering Task Force).
As a industry best practice, you should disable the old protocols which are vulnerable to attacks and update your servers to support the latest protocols. As of June 30, 2018, all websites will need to be on TLS 1.1 or higher in order to comply with the PCI Data Security Standard (DSS) also known as PCI compliance.
How to Check if SSL and TLS 1.0 Protocols is still enabled on your site
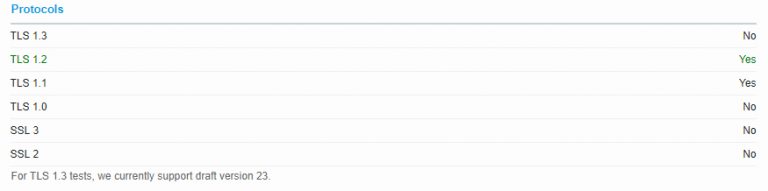
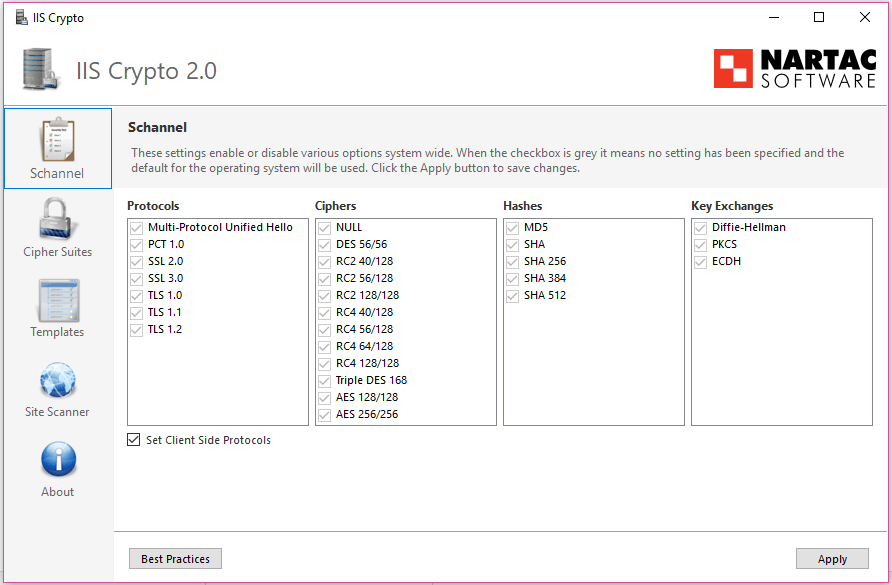
In order to check whether your server still supports the vulnerable protocols, you can use Qualys SSL Server Test. Type your domain name to test and once the test is completed, scroll down to the protocols section and you’ll see a list of all the protocols and their status. Below is an example of a client site I tested and I can say that the administrator has maintained the server very badly, since it still supports SSL 2.0, SSL 3.0, and TLS 1.0 and doesn’t support TLS 1.2. I then logged into the server and ran a GUI tool and below is the status of the protocols (which means all protocols supported by the OS is enabled), which is really bad.

Enable/Disable SSL/TLS Protocols
In order to disable the old protocols (TLS 1.0 and all SSL versions), I downloaded a GUI tool named NARTAC IIS CRYPTO which comes very handy for system administrators instead of editing the registry settings. Below is a screenshot of the software used to enable/disable the protocols. After enabling/disabling the protocols, you need to apply and restart the server in order for the changes to be applied system wide.
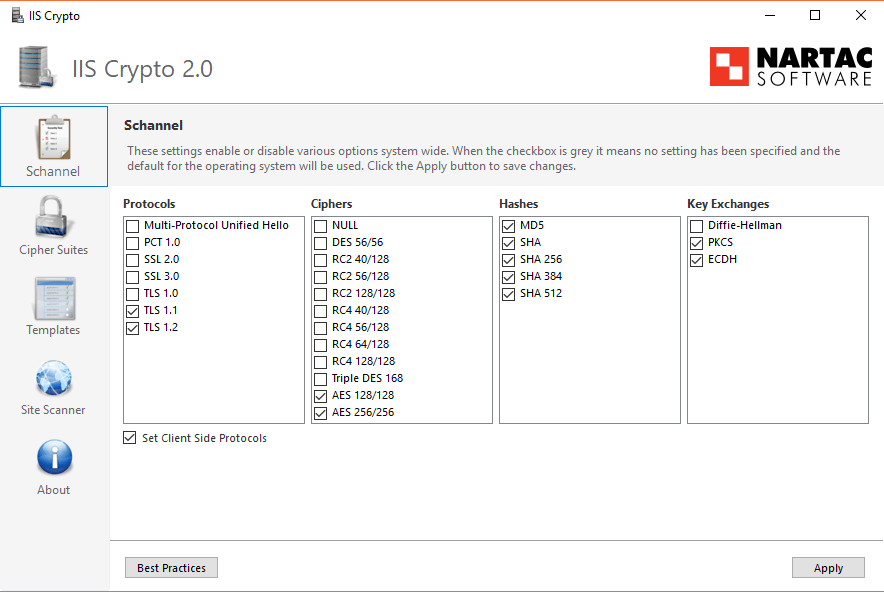
After the changes is applied and system/server restarted, I again checked the site on Qualys SSL Server Test and below is the server configuration with proper protocols enabled.